Passwords
Notes
- Let's explore passwords a bit.
- How does a password work (human level)?
- We assume that the system has a stored copy of your password
- It challenges you by asking you for this password
- It then checks to see if the password you gave it matches the password that is stored.
- This is not right, but it will do for now, we will investigate this further later.
- Right now, we are worried about the threat of someone discovering your password.
- Let's assume that you haven't done anything silly like making your password you dog's name.
- We will investigate a tool to exploit this soon.
- Why does the university have these rules?
- A brute force attack on a password is an attempt to try all passwords
- Is this feasible?
- As a programmer, could you generate all
- 1 letter passwords
- All 2 letter passwords?
- Let's take a look at some code
- cryptSpeed.cpp.
- crypt is a the function that creates an "encrypted" linux/unix password.
-
string.c_string() takes a c++ string and returns a c style string.
-
rand() produces a random integer between 1 and RAND_MAX
-
srand seeds the random number generator.
- You can ignore the
chrono parts
- Let's do an experiment with passwords
- Start excel or any spreadsheet
- On your desktop or online, through "email"
- Constants
- In Cell A2 put "Alphabet Size"
- In Cell B2 put 26
- In Cell A3 put "Processor PPS"
- In cell B3 put 150,000
- This is the value I got on Mirkwood for passwords per second
- In A4 put "Processors"
- In B4 put 1
- In A5 put "Passwords Per Second"
- In B5 put = B3*B4
-
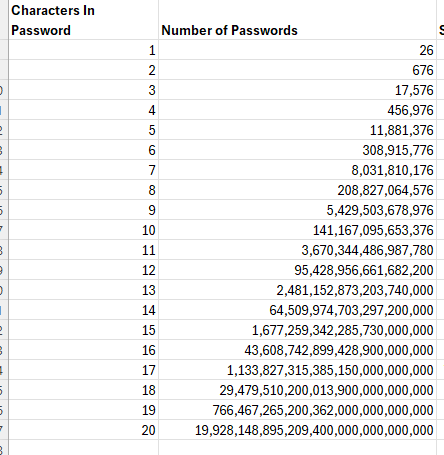
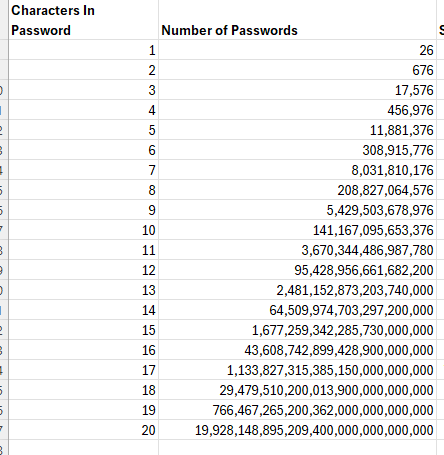
- Number of passwords
- In cell A7 put "Characters in Password"
- In cell B7 put "Number of Passwords"
- In A8 put 1
- In B8 put =$A$2^A8
- explain this formula
- Copy These two down, possibly up to 20 characters in a password
-
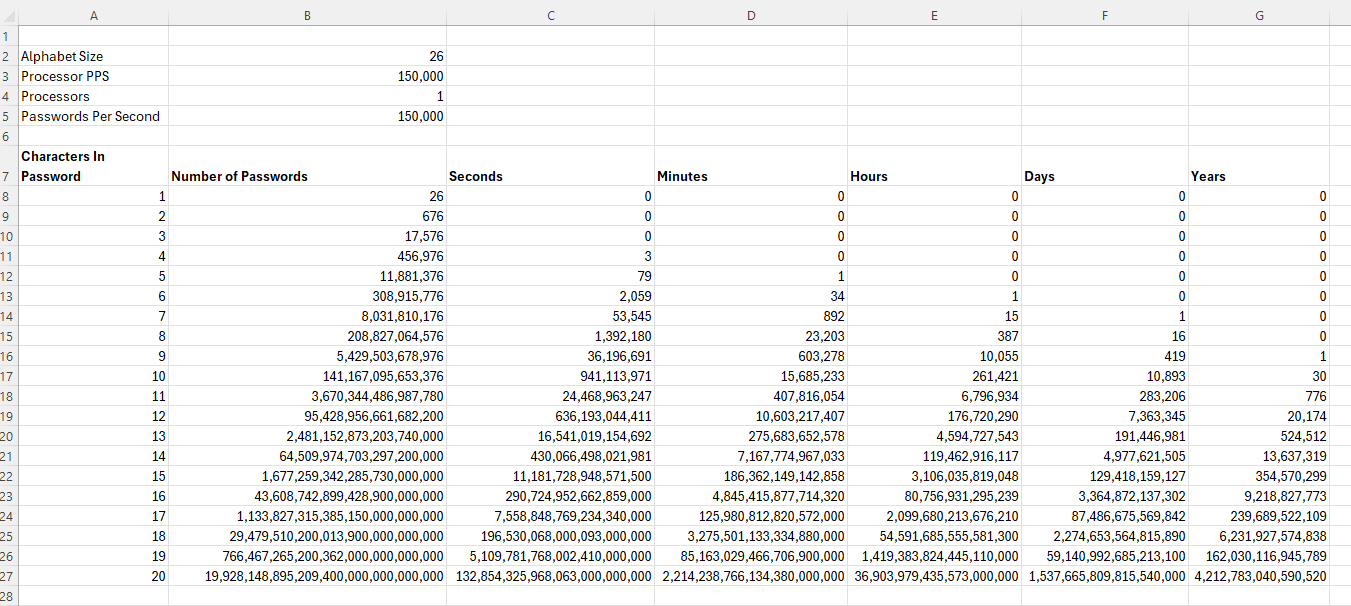
- Time Involved
- In C7 put "Seconds"
- In D7 put "Minutes"
- In E7 put "Hours"
- In F7 put "Days"
- In G7 put "Years"
- In C8 put =B8/$B$5
- Explain this
- In D8 put =C8/60
- In E8 put =D8/60
- In F8 put =D8/24
- In G8 put =D8/365
- Explain this
- Copy these cells down...
-
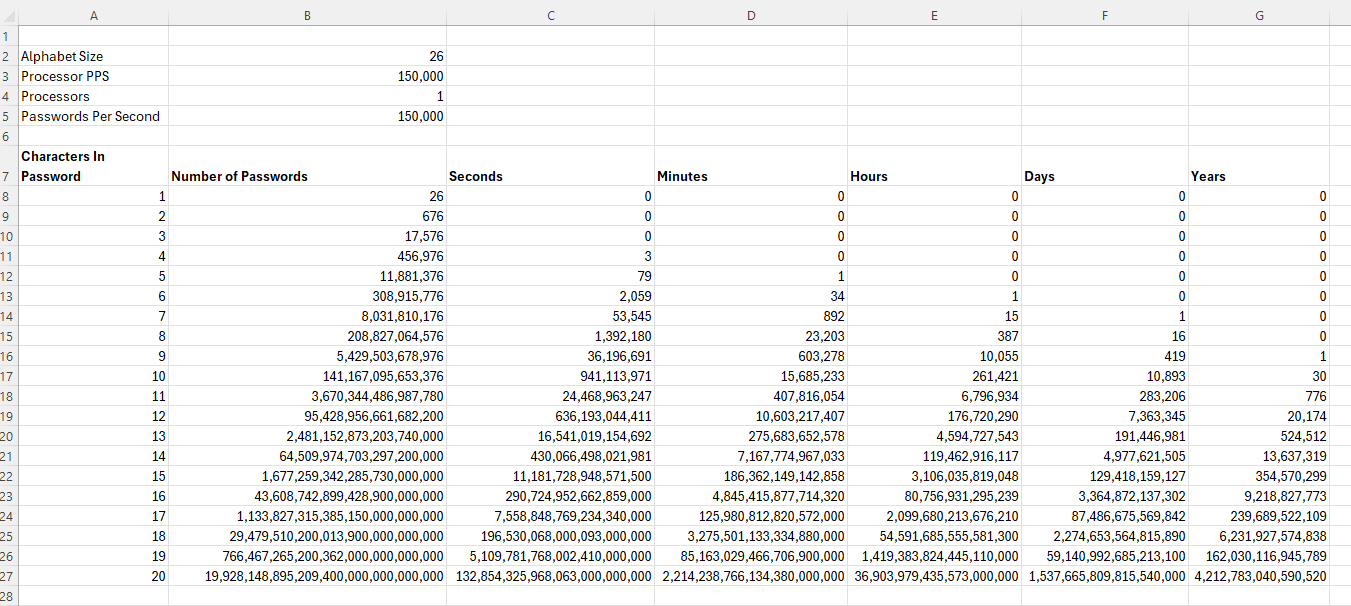
- Adjust the parameters
- Cell B2 represents the number of letters in the alphabet to choose from.
- How do the campus rules change this?
- Cell B4 represents the number of cores involved in a computation
- Is 1 reasonable for this?
- Explain how the number of characters in the password and the number of letters in the alphabet it is chosen from impact the security of a password.
- Take a look at Critical New Password Warning -- Hack Uses 2.8 Million Devices To Attack, Forbes 2025