How passwords have changed
Notes
- A quick overview of passwords in unix
- Originally unencrypted/hashed passwords were stored in /etc/passwd
- File permissions needed to be correct
- Editors frequently make back up copies and these need to be secure
- Nothing to prevent administrators from doing silly things.
- Backups are problematic
- Mistakes were very expensive to fix
- Passwords wiped out, everyone had to reset
- Encrypt passwords
- But reversing an encryption is a problem.
- Remember, we want this automated
- So the key must be stored.
- And many encryption techniques are breakable
- So the password was used as a key, and a constant phrase was encrypted.
- Just decrypt with the password and see if the constant phrase was produced, the password was right.
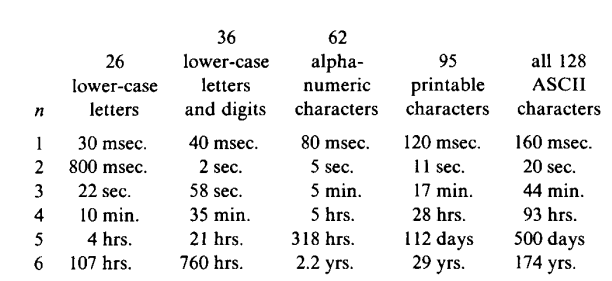
- Back in the 70s, you could check a password every 1.7ms, or 1700 password a second.
- Thompson does the calculation we did
-
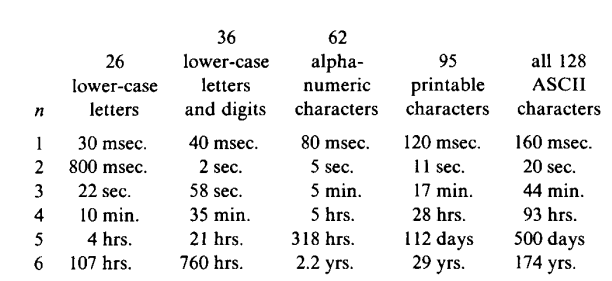
- n = the number of letters in the password
- So a brute force attack was feasible for many cases.
- He also did a study on 3,289 passwords
- 86% were easily guessable
- We will look at this later.
- They tried a slower encryption algorithm
- But machines get faster.
- This is still used today, as we saw last time
- They added a salt (as we saw last time)
- The salt was generated by looking at the system time.
- They looked at the bottom 12 bits
- This gave 212 = 4096 salts (as we saw in the man page)
- The salt is stored as part of the password (as we saw last time)
- The salt
- Each password needed a unique attack, but the salt is known
- It becomes difficult to precompute all possible passwords (rainbow table)
- The original unix password hash was very weak
- Only 8 characters of the password were used.
- It relied on computation speed to partially maintain security
- With a 2 character salt, there were only 4096 different crypts per password
- And only 7 bits of this counted, ASCII
- And only 11 characters in the hash (excluding the salt) or 213*7 possible hashes
- The DES aglorithm was used, but special DES hardware was built.
- We will eventually discuss DES and its problems.
- Over time multiple schemes have been introduced and discarded.
- Hash functions continue to be invalidated and new ones discovered.
- We will look at MD5 is some detail soon
- The hash was stored in /etc/passwd until the mid 80's
- Since this file was public readable everyone could get the hash
- And off site brute force attacks on a single hash
- Moving passwords to a different file (/etc/shadow) is a control for this vulnerability
- The password file needs to be readable by everyone
- The shadow password needs to be readable by root (we will discuss this further)