Ciphers
Notes
- This is from Du: Computer and Internet Security
- A cipher is an encryption/decryption algorithm pair
- Du states that we know of ciphers existing as early as 1900 bc.
- Taterka, Filip. "Ancient Egyptian Royal Cryptography in the Ramesside Period." ANTROPOLOGIA KOMUNIKACJI. (2015): 71.
- A link to the article in English
- It seems to rely on minor changes to words written in hieroglyphics
- Which were very complex and few could read
- And it took an "outstanding" scribe to figure out the real meaning
- I don't know enough about hieroglyphics to completely understand.
- But the paper says they would:
- Change the traditional shape of a hieroglyph
- Change the phonetic value of a hieroglyph
- Add additional signs
- More traditionally ciphers have been characterized as
- Substitution Ciphers: change the meaning of a letter or group of letters
- Caesar Cipher, to encrypt add 3 to each letter a->d, b->e
- Transposition Ciphers: Rearrange the letters
- Playfair Cipher: Build a code block, read the letters from that block.
- Substitution Ciphers: change the meaning of a letter or group of letters
- There is no reason to just have one of these methods.
- And we can do other things as well.
- The simplest is something like a substitution cipher
- Ceaser Cipher
- letter = (letter + 3) % 26, letter = (letter - 3) % 26
- Rot13
- Letter = (letter + 13) % 26
- Keyword-Key Phrase Cipher
-
remove duplicate letters from the key write down the key for letter = a to z if letter has not been written down write it down encrypt based on this code block
- Keyword: edinboro
-
Plaintext Alphabet a b c d e f g h i j k l m n o p q r s t u v w x y z Ciphertext Alphabet e d i n b o r a c e f g h j k l m r s t u v w x y z - Plaintext: Attack at dawn!
- Ciphertext: Etteif et newj!
-
- Or even "The Dancing Man Code".
- Used in a Sherlock Holmes Story, The Adventure of the Dancing Men
-
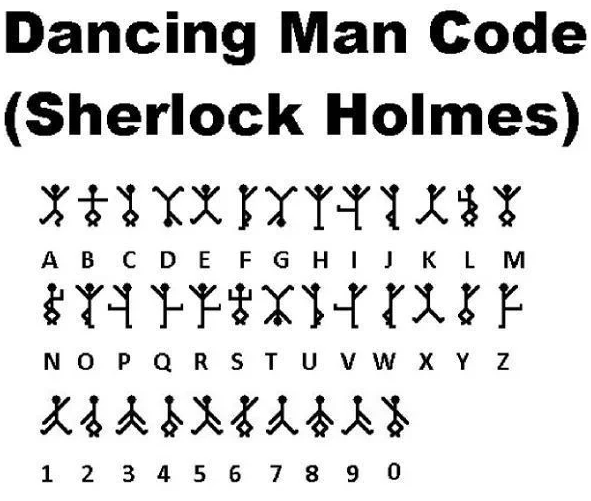 (From https://evil.fandom.com/wiki/The_Dancing_Men?file=Dancing_Men.jpg)
(From https://evil.fandom.com/wiki/The_Dancing_Men?file=Dancing_Men.jpg)
- Ceaser Cipher
- These are all examples of monoalphabetic substitution ciphers
- They are characterized by a simple substitution table.
- Each letter is mapped to exactly one other letter.
- They are, unfortunately, easy to break.
- Frequency analysis
- We know that not all letters in English are used equally.
- see This frequency table, which I reproduce
-
Letter Count Frequency Letter Count Frequency E 21912 12.02 M 4761 2.61 T 16587 9.10 F 4200 2.30 A 14810 12 Y 3853 2.11 O 14003 7.68 W 3819 2.09 I 13318 7.31 G 3693 2.03 N 12666 6.95 P 3316 1.82 S 11450 6.28 B 2715 1.49 R 10977 6.02 V 2019 1.11 H 10795 5.92 K 1257 0.69 D 7874 4.32 X 315 0.17 L 7253 3.98 Q 205 0.11 U 5246 2.88 J 188 0.10 C 4943 2.71 Z 128 0.07 - Or digraphs (From https://pi.math.cornell.edu/~mec/2003-2004/cryptography/subs/digraphs.html)
Digraph Count Digraph Frequency th 5532 th 1.52 he 4657 he 1.28 in 3429 in 0.94 er 3420 er 0.94 an 3005 an 0.82 re 2465 re 0.68 nd 2281 nd 0.63 at 2155 at 0.59 on 2086 on 0.57 nt 2058 nt 0.56 ha 2040 ha 0.56 es 2033 es 0.56 st 2009 st 0.55 en 2005 en 0.55 ed 1942 ed 0.53 to 1904 to 0.52 it 1822 it 0.50 ou 1820 ou 0.50 ea 1720 ea 0.47 hi 1690 hi 0.46 is 1660 is 0.46 or 1556 or 0.43 ti 1231 ti 0.34 as 1211 as 0.33 te 985 te 0.27 et 704 et 0.19 ng 668 ng 0.18 of 569 of 0.16 al 341 al 0.09 de 332 de 0.09 se 300 se 0.08 le 298 le 0.08 sa 215 sa 0.06 si 186 si 0.05 ar 157 ar 0.04 ve 148 ve 0.04 ra 137 ra 0.04 ld 64 ld 0.02 ur 60 ur 0.02 - Or even higher
- Most common bigrams: th, he, in, en, nt, re, er, an, ti, es, on, at, se, nd, or, ar, al, te, co, de, to, ra, et, ed, it, sa, em, ro.
- Most common trigrams: the, and, tha, ent, ing, ion, tio, for, nde, has, nce, edt, tis, oft, sth, men
- Let's break a simple encryption
- I like this working tool..
- This tool would be helpful for computing ngrams.
- I use this site quite frequently.
- Here is a coded message:
Oz Hfypfbc giuk cip fcksue, abk tbyk feu yftu fcg kpbtt, Oz dfpaue giuk cip duut oz feo, au afk ci yqtku cie sbtt, Pau kaby bk fchaieug kfdu fcg kiqcg, bpk jizflu htikug fcg gicu, Deio dufedqt peby pau jbhpie kaby hiouk bc sbpa iwmuhp sic; Unqtp I kaieuk, fcg ebcl I wuttk! Wqp B sbpa oiqecdqt peufg, Sftx pau guhx oz Hfypfbc tbuk, Dfttuc hitg fcg gufg.
- Can you break this coded message?
-
Nsjr-Waec V.I. Jputsgys A gsxst npu p uajv eiagz nbttc rbt aensjr P nopjj katv uajj vtbw rtblsg vspv rtbo p kbfzi uaeibfe sxst ipxagz rsje nbttc rbt aensjr
Not the message is much smaller - AND it does not use the common letter distribution.
-
- Here is a challenge:
-
Xr jr, pf ecx ww of, hyox la gis hiivbvpb: Nviwprs 'hzg rrjyff zb xkm zjbu hs vcsgsi Hlh ayjbxg eql nsffkw rn bvhiokhwht tffxxvr, Pf kc xdsr bfdg ejivogk o whi bg hicyetrt Oer fb wcqcjwrj mae hysq. Ww qjs-kc womrq, Bf asum; nor sm e vtrfd kc wdg jf ser Xkm ufoih-efpr bbu hlh bupijorg vnuiiop vpbdyj Hldb smsjv mv prjf kc: 'xla n dcegypunuwfb Hhdbvhcm xr jr xwjv'h. Ww qjs, kc womrq; Hf gphmc, qsiqldvpf hf rvhiz-bm, kvium'f uvv fye:
-
- Some other tools