Polyalphabetc Substitution Ciphers
Notes
- The first two messages in the previous set of notes were not too bad to break
- Shorter is harder
- Different words/ letter frequency is harder
- Removing spaces, transmitting as a block is harder.
- But in general, this can be done.
- The last message in the previous notes could not be broken with frequency analysis.
- This is because it was not encrypted with a monoalphabetic substitution cipher.
- It was encrypted with the Vigenere cipher (vi-j-ne-are)
- This is a polyalphabetic cipher.
- Or a cipher where each letter is encrypted with a potentially different alphabet.
- Or shift of the alphabet in this case.
- Vigenere takes a keyword and a plaintext message
- In the simple form, each letter is encrypted with shift amount determined by a different letter in the key.
- The message : send more money.
- The key: edinboro
- s -> 's' + 'e'-'a' = 'w'
- e -> 'e' + 'd'-'a' = 'h'
- n -> 'n' + 'i'-'a' = 'v'
- d -> 'd' + 'n'-'a' = 'q'
- space -> space
- m -> 'm' + 'b'-'a' = 'n'
- o -> 'o' + 'o'-'a' = 'c'
- r -> 'r' + 'r'-'a' = 'i'
- e -> 'e' + 'o'-'a' = 's'
- space -> space
- m -> 'm' + 'e'-'a' = 'q'
- o -> 'o' + 'd'-'a' = 'r'
- n -> 'n' + 'i'-'a' = 'v'
- e -> 'e' + 'n'-'a' = 'r'
- y -> 'y' + 'b'-'a' = 'z'
- Note that multiple letters map to q, r, ...
- There are advanced methods for breaking this, but they are much more complex.
- And mostly involve finding the key.
- Since this will generate the same random stream
// encryption initialize the random number generator to a known quantity for each plainLetter in the message offset = plainLetter -'a' cryptLetter = 'a' + (offset + rand() ) %26 // decryption initialize the random number generator to a known quantity for each plainLetter in the message offset = plainLetter -'a' cryptLetter = 'a' + (offset - rand() ) %26 - In this case, the key is the seed to the random number generator.
-
 (Bennett)
(Bennett)
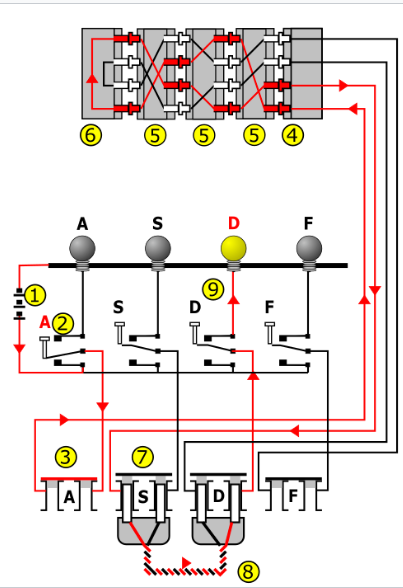
- Used by Germany in WWII
- Polyalphabetic Cipher
- Message (plain or crypt) is typed in on the kyboard.
- The encryption/decryption appears in the lights above the keyboard
- Each day, a key is entered
- Select the roters
- Actually, first select n from a set of M roters
- 3/5, M depended on the version of the machine and branch of service
- Put the roters in the proper order.
- These were usually stored in a codebook, that was required for operation.
- And the wires on the plugboard are changed
- Finally, for each message , and indicator group was set, ie put the roters in the proper position.
- Select the roters
- The roters served as a simple letter mapping
- All roters of a type (I) were the same, and would map, E->T (example, might not be right)
- Ie a simple substitution cipher
- But each time a letter was coded/decoded the roter stepped providing a different alphabet for the next letter.
- Depending on a roter, this would then step the next neighbor by o or more steps.
- The middle roter might step once every 26 letters
- Some roters were designed to step more than one step
- The plugboard provided an additional letter swapping.
- All of these led to 158,962,555,217,826,360,000 different settings
- Chose 3 roters from 5 : 5 * 4 * 3 = 60
- 26 different positions per roter: 263 = 17,576
- 26! different plugboard combinations : 150,738,274,937,250
-
 (Wikipedia, MesserWoland, CC BY-SA 3.0)
(Wikipedia, MesserWoland, CC BY-SA 3.0)
- But the Allies broke it
- Bad design: a letter could not map its image a->a is forbidden
- This gave cryptoanalyists a way to remove a number of rotor order combinations
- Any combo where letter->letter was discarded
- Bad use: the initial letter settings were sent before the message
- This gave cryptoanalysts a way to remove some possible initial rotor positions
- And a clue into some possible initial positions
- Not all roters incremented by the same amount
- This also helped determine rotor location
- Only resetting the machine once a day
- Provided more messages for decryption
- Some letters were re-transmitted as themselves (special characters)
- Provided insight into the messages
- And some spy work (1931-1932)
- Bad design: a letter could not map its image a->a is forbidden