Lab: John the Ripper.
The goal of this step is to setup for the lab.Step 3: John Operation
- Remember there is documentation for john.
- Run john on the password file
- john comes with an
unshadowutility- This will make the password file usable by john.
- Run this
-
sudo unshadow /etc/passwd /etc/shadow > myPass
-
- Look at myPass
- Each line represents a user.
- Run john on this file
-
john myPass - Notice this returns almost instantly. Read the text john produces.
- Run
john myPass --show - This tells you that john has figured out the passwords for bob and alice.
- This is not a surprise as the first pass of john is to try information from the password file.
-
- If you run john again, it will not do anything
- John is designed as a long term continuous operation.
- It saves a history of the passwords it has found
- Look at the files in ~/.john
-
ls ~/.john -
less ~/.john/john.log -
less ~/.john/john.pot
-
- john comes with an
- In the setup we downloaded and build
myCryptwhich will create a fake password file entry given a user name and a password.- try
./myCrypt user1 hello - As we saw in the pwnkit lab, we can redirect output to a file with the > and >> operators.
- try
./myCrypt user1 hello >> newPassFile- Look at the contents of newPassFile
- run
john newPassFile- This will return instantly so
- run
john --show newPassFile
- try
- Using the command above add a few more entries to newPassFile.
-
Username Password user2 hell0 user3 hello1 user4 passwords user5 are user6 fun user7 to user8 crack kirk ncc1701 pickard ncc1701d
-
- Now try running john
-
john newPassFile - At any time, you can press a key to see what john is working on.
- This includes
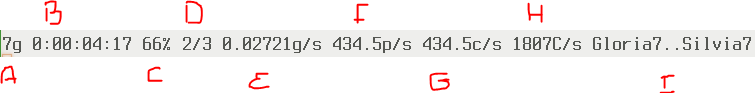
- The number of passwords guessed
- The length of time John has been running (D-H-M-S)
- Percent done on the current pass.
- Which pass it is on
- Guess per second rate
- Passwords per second
- Crypts per second.
- The current words being tested.
- This includes
- Note that within a minute or two John has guessed most of the passwords.
- We can help John out by giving it a different dictionary.
- Try
john --wordlist=lower newPassFile- This tells john to use the file lower to check.
- Note that in a few minutes the other two passwords are found!
- You don't need to wait for the entire process to complete.
-
- Strangely, to is the hardest of this set to crack, but that is just an accident of the alphabet.
- At 400 PPS, it will take no longer than 12 minutes to find that one however.
- This will not work well on your simulated machine, but it will work.
- John works in parallel mode.
- Start by removing the .john directory in bob's home directory
- Remember, john caches the passwords it has found in this directory
- By removing this directory, you force john to start over.
- Be careful and do this right
-
rm -rf ~/.john
-
- Start john again but this time
-
john newPassFile --wordlist=lower --fork=2 - Try pressing the space bar now and monitor John's progress.
- You don't need to wait for the entire process to complete.
- On Mirkwood, with 4 real cores, it took nearly four minutes to find all these passwords
[bennett@mirkwood pass]$ time john newPassFile --wordlist=lower --fork=4 Created directory: /home/bennett/.john Loaded 10 password hashes with no different salts (crypt, generic crypt(3) [?/64]) Node numbers 1-4 of 4 (fork) Press 'q' or Ctrl-C to abort, almost any other key for status are (user5) crack (user8) fun (user6) hello (user1) passwords (user4) to (user7) 4 3g 0:00:03:49 100% 0.01309g/s 323.7p/s 323.7c/s 2684C/s zoologies..zyzzyva 1 1g 0:00:03:49 100% 0.004355g/s 323.1p/s 323.1c/s 2970C/s zoologist..zyzzyvas Waiting for 3 children to terminate 3 2g 0:00:03:49 100% 0.008707g/s 323.0p/s 323.0c/s 2882C/s zoologize..zythum 2 0g 0:00:03:51 100% 0g/s 320.1p/s 320.1c/s 3201C/s zoologists..zythem Use the "--show" option to display all of the cracked passwords reliably Session completed real 3m51.805s user 15m18.599s sys 0m0.037s
-